Hacker Sells Access Codes for 20 Million OpenAI Accounts
In a digital world where security is evolving, the latest alarm comes from an alleged sale of 20 million OpenAI account credentials by a hacker going by the name emirking. If true, this massive breach could open the door to unauthorized access of sensitive user data, including conversations, calls, and API usage. Let’s break down the claims, the expert analysis, and what you can do to protect yourself.
The Digital Heist: 20 Million Credentials up for Grabs
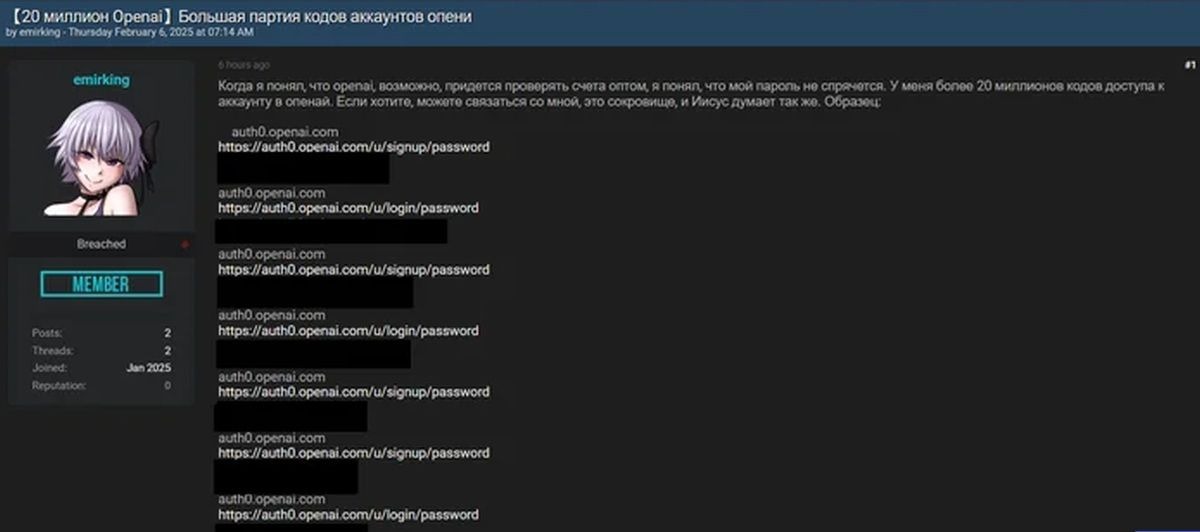
Late last month, a post appeared on the BreachForums hack forum, where emirking offered a “treasure” of OpenAI credentials. The hacker claims these access codes can bypass OpenAI’s authentication, potentially exposing user data.
It is unlikely that such a large amount of accounting data could be collected during phishing operations. Therefore, if the statement of the attacker is true, emirking could find a way to compromise the auth0.openai.com subdomain, taking advantage of the vulnerability or having received the authority of the administrator.” — Malwarebytes Analysts
This claim raised immediate red flags. The sheer volume of credentials—20 million—suggests a more systematic approach than a single phishing campaign.
Potential Impact: Phishing, Fraud, and API Abuse
Should these credentials indeed grant unauthorized access, the implications could be far-reaching:
- Phishing Campaigns: Attackers could leverage user information to craft highly targeted scams.
- Financial Fraud: Personal details extracted from chats or calls might be used to orchestrate fraudulent transactions.
- API Exploitation: Access to the OpenAI API could be abused, leading to unauthorized usage or billing charges.
However, BreachForums users who tested the sample credentials noted that they did not allow access to archived ChatGPT conversations, suggesting the breach may be less extensive than claimed—or that the data is incomplete.
Expert Analysis: Aggregated Data, Not a Direct Breach?
Malwarebytes and Kela researchers believe these access codes likely originated from a broader dataset compiled by information stealers rather than a targeted hack on OpenAI. Infostealers like Redline, RisePro, StealC, Lumma, and Vidar are known for gathering user credentials from various platforms and packaging them into large, aggregated dumps. Kela's Findings were the samples match other known data sets from infostealers and the first hacker message on BreachForums correlates with “style logs” typically seen in these large-scale credential leaks.
In other words, it appears the hacker may be reselling or repackaging credentials already circulating in underground marketplaces.
OpenAI’s Response: Investigation Underway
OpenAI representatives have stated that they take these claims seriously. Thus far, internal investigations have not revealed any direct compromise of OpenAI systems:
We take such statements seriously. At the moment, we have not identified any evidence or connection with the hacking of OpenAI systems..” — OpenAI Spokesperson
Here was the last time OpenAI experienced a large data breach.
This underscores the likelihood that the hacker’s claims might be exaggerated, or at least not indicative of a direct, large-scale breach of OpenAI’s infrastructure.
Conclusion: Securing Your Digital Future
The story of 20 million OpenAI credentials for sale serves as a reminder that, in our interconnected digital world, data can be collected and repurposed in countless ways. Even if OpenAI itself remains secure, third-party breaches or aggregated datasets can still pose a risk to unsuspecting users. Here are few suggestions for maintaining a secure account.
- Use unique, strong passwords for every platform.
- Enable multi-factor authentication wherever possible.
- Monitor your accounts for unusual activity and be vigilant about phishing attempts.
Ready to Strengthen Your Security?
Schedule your consultation and let us help you design a robust strategy that protects your digital assets and keeps your business running securely.
%20(1).png)

%20Sam%20Altman.jpg)















